How OTT platforms can prevent content piracy at scale

A growing regional OTT platform uploads a new exclusive title on a Friday morning. By Friday afternoon, the full-length file is on three Telegram channels and a piracy forum. The platform spent four months negotiating content rights and two weeks marketing the release. The pirate spent 90 minutes with a screen recorder.
Now run the math. 100,000 potential viewers for the release. Even a conservative 15% piracy diversion means 15,000 viewers who watched for free. At $5 average revenue per user, that's $75,000 gone from a single title. Multiply across 8-10 releases per month, and you're looking at $600,000 to $750,000 in annual leakage. For a regional platform operating on thin margins, that's the difference between growth and shutdown.
On March 25, 2026, the US Supreme Court ruled that ISPs are generally not liable for their users' copyright infringement. The burden of protecting content now falls squarely on the platform. And the tool most platforms reach for first, DRM, solves only one piece of the problem.
Content piracy at OTT scale is a speed and systems problem, not an encryption problem. Isolated tools (DRM alone, signed URLs alone, geo-blocking alone) each address one attack vector while leaving others wide open. Effective protection requires four coordinated layers: access control (JWT auth with token rotation, signed URLs), encryption/DRM (Widevine, FairPlay, PlayReady), deterrence (forensic watermarking), and detection/response (automated monitoring, DMCA takedowns).
Key takeaways:
The piracy threat facing a regional OTT platform in 2026 is fundamentally different from what it was five years ago. The attack surface has expanded in ways that individual tools can't cover.
Global piracy website visits hit 216 billion in 2024, up from 130 billion in 2020 (MUSO, cited by The Guardian). That's not a slow trend. That's acceleration. And the Asia Video Industry Association (AVIA) flagged AI-driven piracy and decentralized streaming networks as the emerging threats in their 2026 report, meaning the problem is getting more sophisticated, not less.
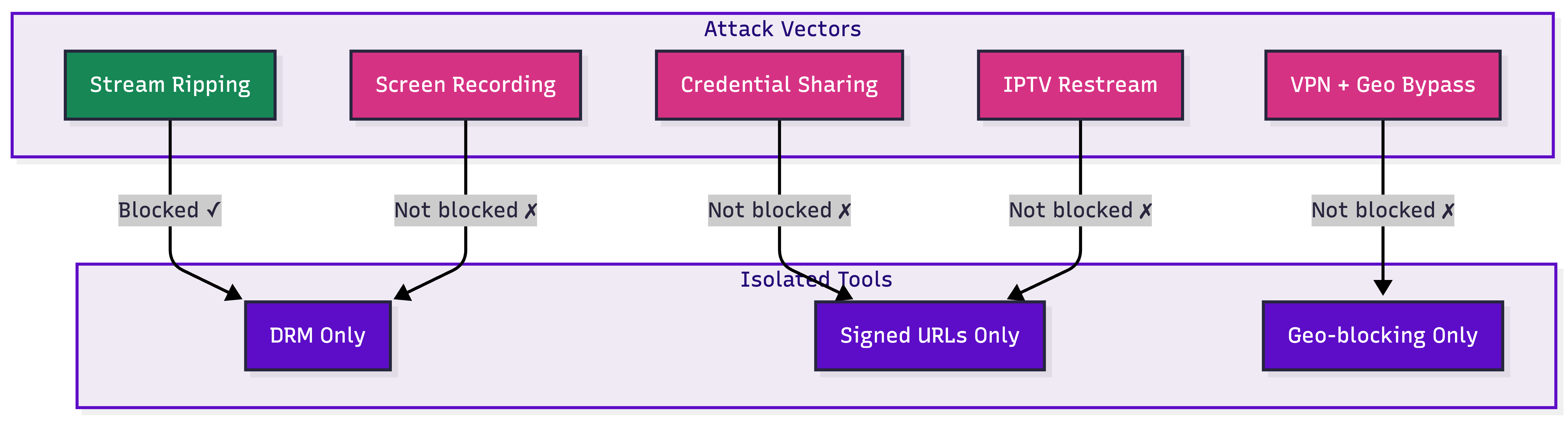
The attack vectors at OTT scale break down into five categories, each requiring a different response:
That table tells the real story. No single technology covers all five vectors. If your content protection strategy is "we have DRM," you're covering one row and hoping the others don't happen. They will.
DRM prevents direct downloading of encrypted video segments. It does not prevent screen recording. This is the analog hole, architecturally unsolvable by encryption. Signed URLs prevent link sharing, but if credentials are shared with 20 people, the URLs are valid because the session is valid. Geo-blocking restricts playback to licensed territories. A VPN bypasses it in under 10 seconds.
According to the decodeTV March 2026 industry survey, DRM and geo-blocking are the most commonly used security techniques, both at 65.6% adoption. Yet 20% of senior video business insiders still characterize piracy as an "Existential" threat, with another 31% calling it "Big." The most widely deployed tools aren't solving the problem.
The issue isn't that these tools don't work. They do, within their narrow scope. The issue is that piracy exploits the gaps between them. We mapped out the full seven-layer security architecture beyond DRM in a separate deep dive. What follows here is the OTT-specific version: four layers designed for platforms where content acquisition costs and licensing obligations make piracy a revenue problem, not just a technical one.
The right mental model isn't "which tool should we buy." It's "how do we design a system where each layer compensates for the limitations of the others."
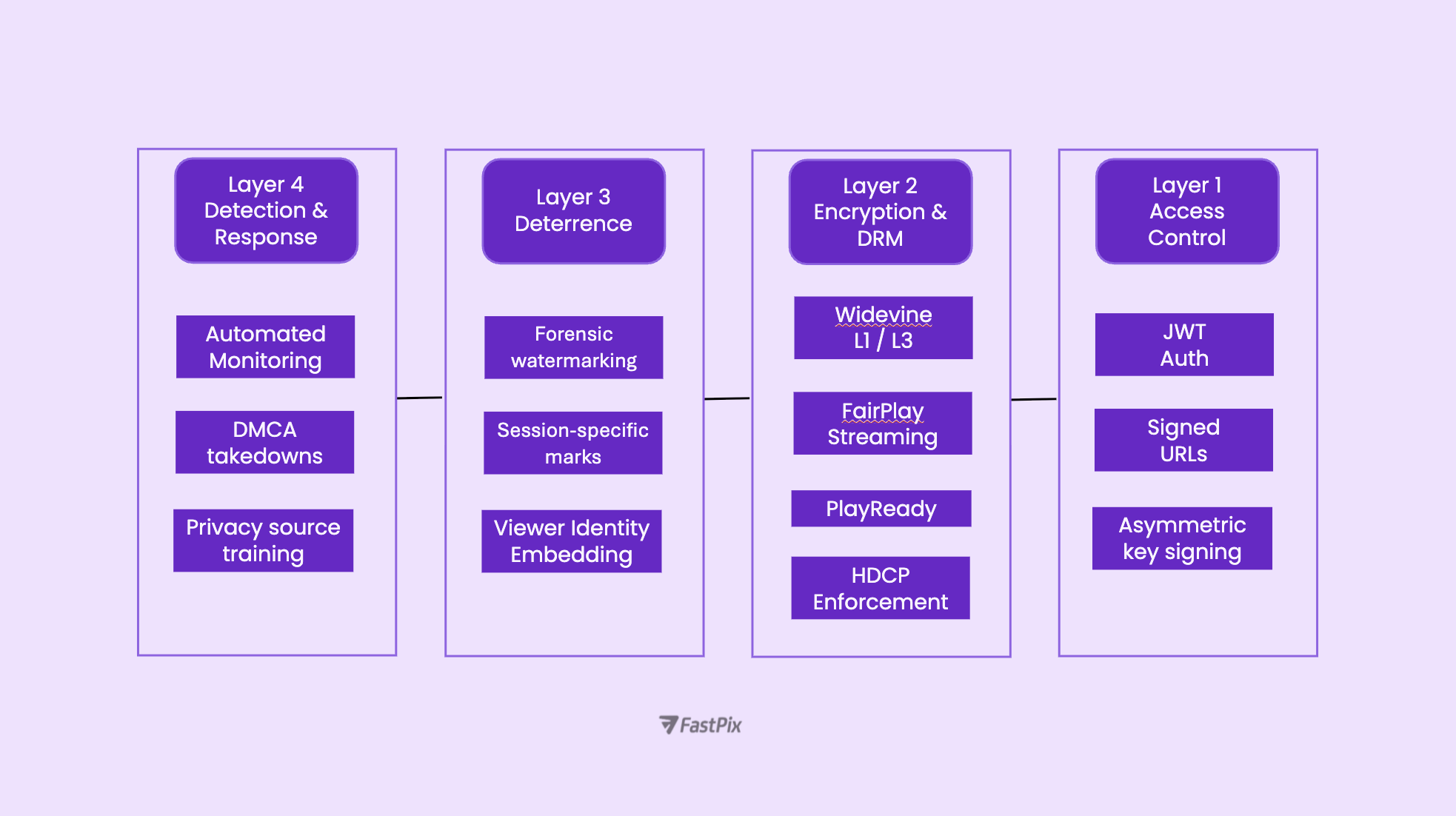
Access control determines who can request playback and under what conditions. This is the highest-ROI layer because it blocks the most common vector (credential sharing) at the lowest cost.
JWT-based playback authentication issues short-lived tokens for every playback session. The token contains the user's identity, device fingerprint, and an expiration timestamp. When rotated frequently, even a leaked token becomes useless within minutes. Credential sharing at scale is one of the largest revenue drains for growing OTT platforms.
Asymmetric key signing strengthens this further. The platform's backend signs JWTs with a private key. Edge servers, CDN nodes, and middleware validate tokens using only the public key. No service in the delivery chain ever needs the signing secret, which means a compromised edge node can't forge valid tokens.
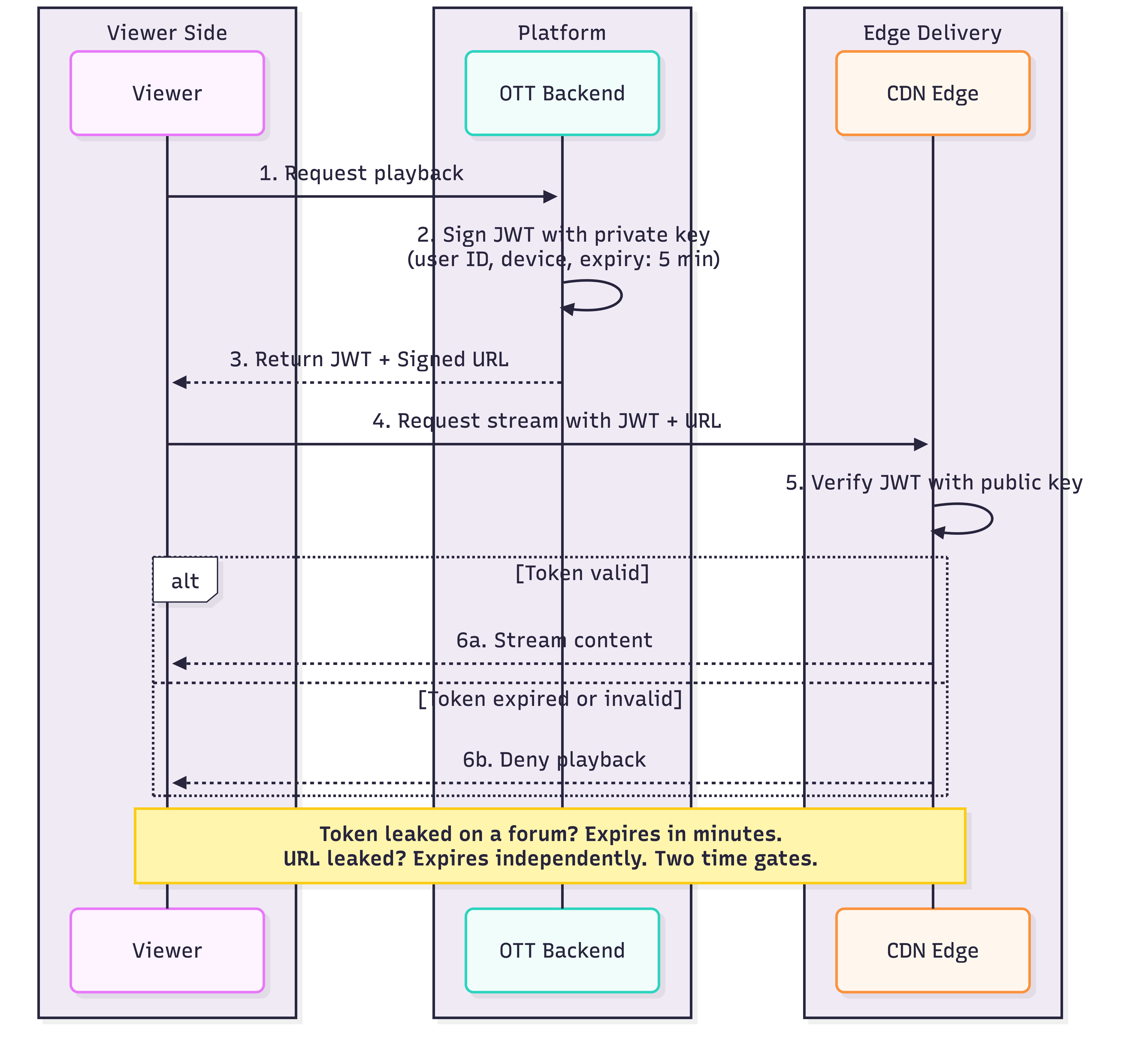
Signed URLs with short expiry windows add a second time gate. Even if a user extracts a playback URL and shares it, the URL itself expires independently of the JWT. Two independent expiration mechanisms make casual sharing structurally ineffective. We break down the full access control implementation for platform builders in how to protect online courses from piracy, and the same architecture applies at OTT scale.
DRM encrypts video segments and manages decryption through a controlled chain: the player authenticates, requests a license, receives a decryption key, and passes it to a Content Decryption Module (CDM) that decrypts frames in a protected environment.
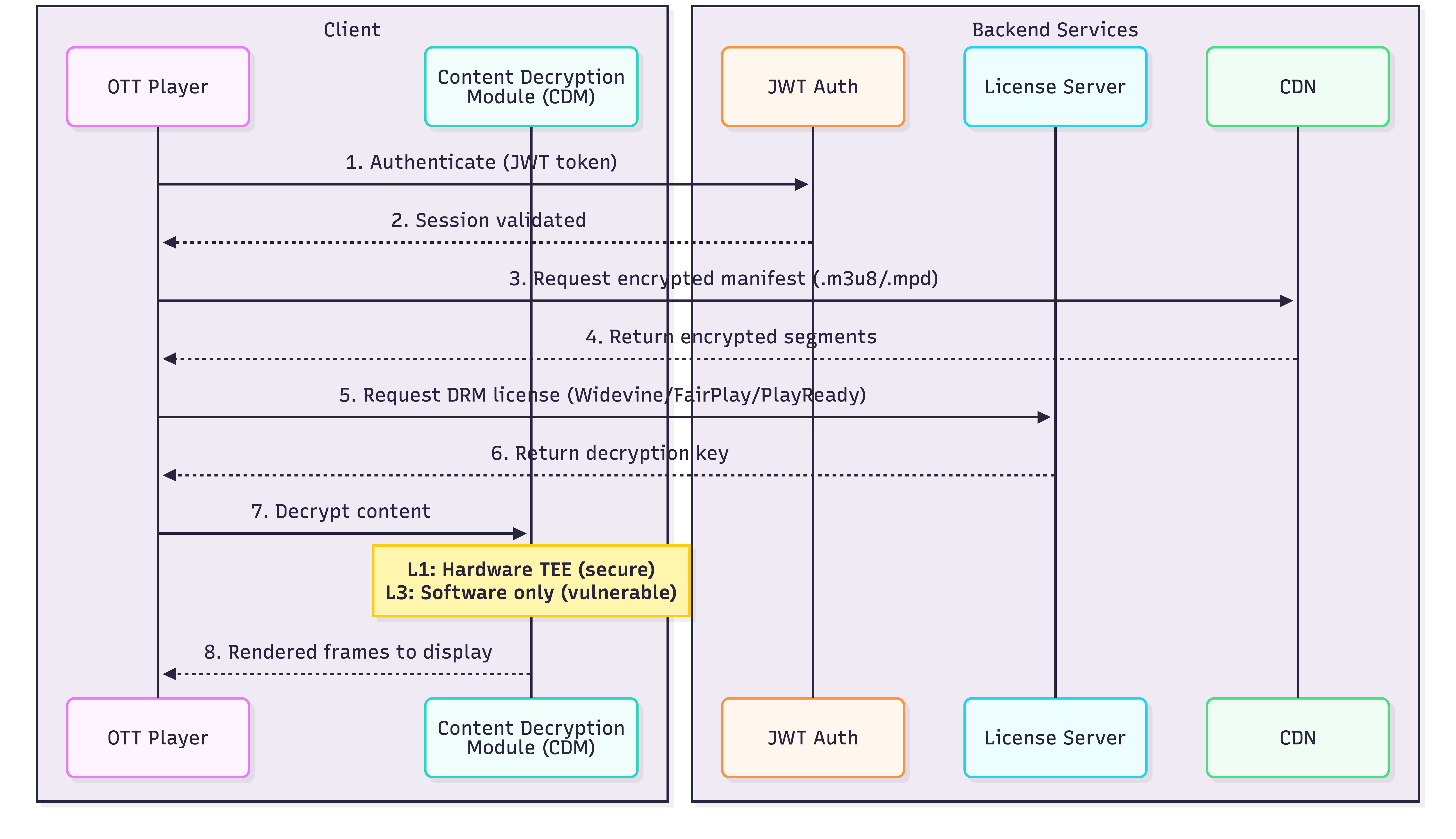
Full device coverage requires three DRM systems: Widevine for Chrome and Android, FairPlay for Safari and iOS, PlayReady for Edge and Windows. Most modern video APIs handle multi-DRM packaging through Common Encryption (CENC), encrypting once and generating both DASH and HLS manifests.
The distinction between Widevine L1 and L3 matters for content licensors. L1 decrypts inside a hardware Trusted Execution Environment (TEE), meaning keys and decrypted frames never enter accessible memory. L3 runs in software and has been reverse-engineered repeatedly. If your licensing agreements require specific security levels (and increasingly they do), you need infrastructure that supports L1 enforcement. We covered why DRM alone leaves critical gaps in DRM is a lock on an open window.
This is where the infrastructure layer matters. At FastPix, Layers 1 and 2 are handled natively through a single API: JWT-based playback authentication with automatic token rotation, asymmetric key signing for distributed validation, signed URL access control, and DRM-ready outputs packaged for Widevine, FairPlay, and PlayReady simultaneously. An OTT team integrating this gets multi-DRM delivery and two layers of time-limited access control without assembling separate encoding, packaging, DRM licensing, and CDN services. The $25 free credits cover roughly 800 minutes of encoded content, enough to validate the full protection pipeline against your own content library before committing.
If Layer 2 is the lock, Layer 3 is the security camera. Forensic watermarking embeds an invisible, unique identifier into each viewer's stream. If content leaks, extracting the watermark reveals exactly which account captured it.
Two approaches exist. A/B variant watermarking produces multiple versions of each segment with slightly different pixel-level modifications at encoding time. The CDN serves the correct variant based on the authenticated session. Server-side composition applies the mark during delivery, modifying segments on-the-fly. Both survive screen recording, re-encoding, and compression.
The Asia Video Industry Association's 2026 report documented this shift in practice. Regional OTT platforms across Southeast Asia that relied exclusively on DRM began layering forensic watermarking into their delivery pipelines after finding that most pirated content came from screen recordings, not stream rips. AVIA noted the move from "passive to proactive enforcement" as a defining trend of 2026, with regional cooperation between platforms and anti-piracy services accelerating takedown response times.
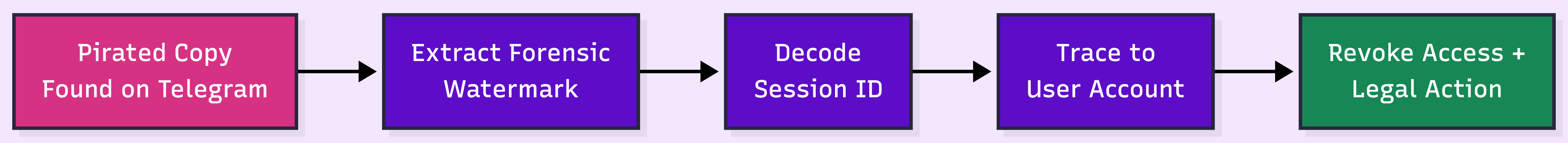
.png)
Watermarking adoption grew 28% across the industry in 2024. The economics are shifting: as content acquisition costs rise, the cost of not tracing leaks becomes harder to justify.
Protection without detection is half a strategy. Content monitoring services continuously scan torrent sites, Telegram channels, cyberlockers, and social platforms using audio/visual fingerprinting to match pirated copies against your originals.
Only about 9% of DMCA takedown requests achieve their goal (Verimatrix, 2026). Offshore hosting and non-compliant intermediaries make individual takedowns a losing game. What works is automated volume: services that file hundreds of notices per day, re-file on re-uploads, and escalate repeat offenders to legal channels.

AI-driven detection is where the industry is heading. OTT adoption of AI-based monitoring grew 52% in 2024, and MUSO's 2026 strategy emphasizes "always-on, automated monitoring" combining AI crawlers with expert verification. Manual, reactive takedowns are being replaced by automated, continuous enforcement.
For live sports and events, where piracy happens in real-time, the detection window shrinks to minutes. This is where live clipping becomes relevant as a counter-strategy. Authorized clip distribution during live events reduces demand for pirated streams by giving viewers legitimate, shareable moments.
Not every OTT platform needs the full stack from day one. Over-investing in Layer 4 before Layer 1 is solid wastes budget while leaving basic vulnerabilities open.
The revenue-at-risk calculation makes this concrete:
At 500,000 subscribers, even a 10% piracy diversion rate means $3 million in annual revenue loss. That context makes a $50,000/year investment in watermarking look like an obvious decision.
Every layer above depends on the foundation underneath it: the video API that handles encoding, DRM packaging, and delivery. FastPix handles Layers 1 and 2 out of the box, with JWT token rotation, asymmetric key signing, signed URLs, and multi-DRM outputs in a single API.
Piracy doesn't wait for your security roadmap to catch up. The platforms that protect their revenue are the ones that treat content protection as infrastructure, not an afterthought. If you're building or scaling an OTT platform and want to get the foundation right, talk to our team.
Revenue loss depends on subscriber base and content value. A platform with 500,000 subscribers losing 15% of viewers to piracy at $5/month average revenue forfeits roughly $375,000 per month. Global piracy site visits reached 216 billion in 2024 (MUSO), and 20% of video business insiders characterize piracy as existential (decodeTV, 2026). Original and live content face the steepest diversion rates.
No. DRM prevents unauthorized downloading and redistribution of encrypted video files, but it cannot stop screen recording or HDMI capture. This is the analog hole, an architectural limitation every DRM system shares. Platforms that treat DRM as a complete solution leave screen recording, credential sharing, and IPTV restreaming unaddressed.
Forensic watermarking embeds an invisible, unique identifier into each viewer's video stream during encoding or delivery. If content is pirated, the watermark can be extracted from the leaked copy to identify which specific account captured or redistributed it. Unlike visible watermarks that can be cropped, forensic marks survive re-encoding, screen recording, and compression. For OTT platforms, it turns every playback session into a traceable event.
Platforms use automated monitoring services that scan torrent sites, Telegram, and social platforms using audio/visual fingerprinting. OTT adoption of AI-based monitoring grew 52% in 2024. However, only about 9% of DMCA takedowns succeed (Verimatrix, 2026), so automated volume and continuous scanning matter more than individual notices.
Widevine L1 decrypts content inside a hardware Trusted Execution Environment (TEE), meaning decryption keys and video frames never enter accessible memory. L3 is software-only decryption running in the browser, and it has been reverse-engineered multiple times. For OTT platforms with premium or licensed content, L1 provides meaningfully stronger protection. Many content licensing agreements now explicitly require L1 enforcement on supported devices.
JWT-based playback authentication issues short-lived tokens that expire quickly, even if intercepted. Token rotation means each session gets a fresh token with a limited validity window, so a leaked token becomes useless within minutes. Combined with asymmetric key signing, where a private key creates the token and a public key verifies it, distributed systems can validate playback requests at the CDN edge without ever exposing the signing secret. This makes both casual sharing and systematic credential distribution structurally difficult.
